Phishing Vessels

Loki Bot campaign targets maritime industry
DarkLab intelligence analysts detected a Loki Bot phishing campaign targeting the maritime and engineering sectors in Europe, Asia and the US from spoofed email addresses of legitimate organisations in Asia.

Figure 1 – Countries of origin of phishing recipients (blue) and legitimate organisations’ spoofed addresses (red)
Recipients of phishing emails – hard to see in the map above – were also located in Singapore.
The earliest phishing email detected dates back to October 2019. However, our previous research indicates that this threat actor is using maritime themes in their phishing campaigns since at least 2018, and is linked to other malware families including Pony.
The 2019 email was sent from a likely compromised subdomain of an Indonesian company and contained a malicious archive (.rar) attachment purportedly pertaining to a purchase order, a common theme of spam emails.
Since then, the actor behind the campaign refocused their phishing lures by spoofing emails of legitimate organisations linked to the maritime industry, and by referring to vessels and other naval themes in their emails.

Figure 2 – Example of phishing email spoofing a Singapore-based shipping company

Figure 3 – Example of phishing email sent to a Switzerland-based maritime consultancy
Some phishing emails showed a good knowledge of the shipping industry, including believable details of existing ships and ports locations.

Figure 4 – Example of phishing email sent to a Japanese shipping company

Figure 4 – Example of phishing email sent to an Italian engineering contractor, purporting to be from a Chinese port authority
For instance, both vessels mentioned in the email above, Glovis Crown and Glovis Splendor, are 200m long cargo ships registered in the Marshall Islands. It remains unclear how criminals managed to obtain such details, although it seems likely that they derive from previously hijacked communications of potentially unrelated victims.
This second wave of phishing emails has been active between February and late June 2020, suggesting the campaign is likely still active.
Phishing emails switched to a malicious Microsoft Excel (.xlsx) attachment containing an exploit for CVE-2017-11882. This vulnerability in Microsoft Equation Editor lets attackers run remote code on a vulnerable machine when the victim opens a document. The exploit has been actively used by multiple cybercriminal groups due to the level of access it grants to the victim machine and the lack of user interaction needed.
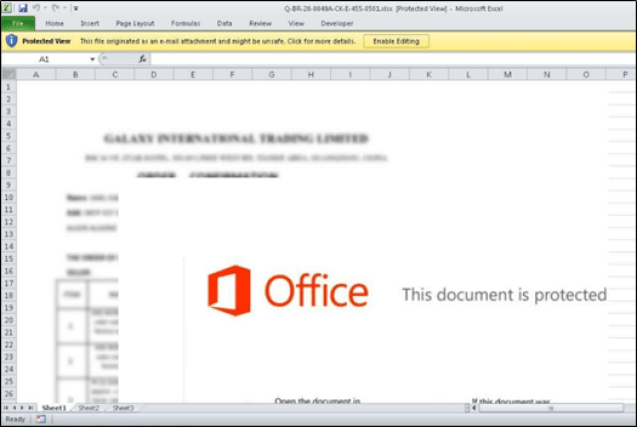
Figure 5 – Screenshot of malicious xlsx attachment to email in Figure 4 [MD5: e7bb1284bf0e723b47435b0f70504b3f]
The malicious documents are downloaders for Loki Bot, an information stealer first seen in 2015. The malicious payloads observed, and additional ones found by pivoting on the attack infrastructure, are downloaded from duckdns.org subdomains likely created with domain generation algorithms (DGA).
The payload, Loki Bot, can steal credentials from browsers and email clients, among other programs, and has keylogging capabilities. The malware also sends identifying information about the victim’s hosts to a C2 to inform threat actors of the successful infection.
The current Loki Bot campaign highlights the ongoing threat of commodity malware and widespread phishing to organisations in the maritime and engineering sectors. Although the campaign exploits well-known threat vectors, lack of widespread adoption of anti-spoofing technologies like SPF and DMARC, or their incorrect implementation, means that criminals can continue sending credible phishing emails apparently from legitimate domains.
Indicators of Compromise
Emails Sender’s IP
103.253.115[.]37
Downloader Domains
russchine2specialplumbingwsdymaterialgh3.duckdns[.]org
chneswealthandorganisationstdy7joppl.duckdns[.]org
12chnesstdywealthandmoduleorganisationrn.duckdns[.]org
chnes14wealthandstdymoduleorganisationoo.duckdns[.]org
chnthreewealthsndy3andreinforcementagenc.duckdns[.]org
20chneswealthandsndymoduleorganisationvz.duckdns[.]org
chnes29sndyqudusisabadassniggainthebba.duckdns[.]org
united32wsdyfrkesokoriorimistreetsjkjd.duckdns[.]org
russchine2sndymapanxmenischangedone14ajb.duckdns[.]org
sndychnesprvlandofglorylandoflifeforle.duckdns[.]org
greenpegheedahatakankeadeshnaajaotawsdy.duckdns[.]org
sndychnesprvlandofglorylandoflifeforle.duckdns[.]org
Payloads
4ae5c9c199377980ebc558d27e7855960c69167138951378666421b9b3db09de
bcc826091ec71230947aa1916263434935a58ffe5977cf415b1d970633939652
58e0c4eef4236380167e9ea679e7885aebb5319dd0ea17365b90b5867cae7ff8
49107c228e38638d3b241bb5c4aa93ef68db20cc0c5a4157e00fc027635418bf
9ea2966982206d42cd8ad215f7a408bf7c1964134e3bef967e7bb93df6dc1f1a
b48f93828a970b7f2122b098cade1e1ab488ef557cf11ae0c44f5690f6c45185
83ba255722d5c337ce128b5e216fc1a4010849b3b4ac3e4841458d371ed757d6
Feel free to contact us at [darklab dot cti at hk dot pwc dot com] for any further information.







