Forecasting the Cyber Threat Landscape: What to Expect in 2023

In a blink of an eye, 2023 is upon us. As we bid farewell to another record-breaking year of increased disclosed vulnerabilities, ransomware incidents, phishing scams, data breaches, and crypto heists, it is hard not to imagine that this year will be any less eventful as threat actors aggressively lower the barriers to entry of “cybercriminalism” by crowdsourcing their tasks. Based on PwC Dark Lab’s observations throughout 2022, we share our assessment of the potentially most prevalent threats and potential trends in the upcoming year.
Hackers will weaponise exploits at an even faster rate and scale to bypass heightened controls, thus achieving near-instant impact beyond initial access
Threat actors have demonstrated their increasing sophistication in speed and scale through the decreased timeframe required to weaponise critical vulnerabilities. In 2022, threat actors were able to weaponise critical vulnerabilities such as Zimbra Collaboration arbitrary memcache command injection (CVE-2022-27924) and FortiOS authentication bypass (CVE-2022-40684) within three (3) days of the Proof-of-Concepts (POCs) being published to perform unauthenticated remote code execution. In extreme cases such as Log4Shell (CVE-2021-44228), we observed that the weaponisation occurred a mere eight (8) hours after public release from our first incident response of the year (read more here).
Part of the reason why threat actors need to go faster is due to improved security controls of service providers. For example, Microsoft announced in February 2022 that Microsoft Office would automatically block Visual Basic Applications (VBA) macros in all downloaded documents by default in a phased rollout approach between April and June. As a result, we observed threat actors expeditiously developing novel exploits to perform client-site execution that bypasses the newly introduced security controls. [1] This includes the Mark-of-the-Web (MOTW) vulnerability (CVE-2022-44698) which allows for specially crafted ZIP and ISO files to be downloaded and executed without undergoing integrity checks on the user’s endpoint. [2] PwC’s Dark Lab has actively responded to an incident in August 2022 that observed the threat actor deploying Magniber ransomware after exploiting the MOTW vulnerability.
Meanwhile, exploit toolkits are not new but are being matured to an extent where threat actors of all sophistication can utilise to achieve near-instant impact beyond just initial access. In the cases of Zimbra (CVE-2022-27924) and FortiOS (CVE-2022-40684), our incident response experience suggests that threat actors likely leveraged exploit toolkits to automatically chain the POC exploit with standardised steps to establish persistence, perform discovery, move laterally, and achieve elevated privileges if applicable. As a result, victims that did not swiftly apply patches or workarounds to mitigate the risks associated with critical vulnerabilities likely needed to conduct intelligence-led threat hunting to ensure that their environment was not further impacted in any way.
We hypothesise that the rate and scale of weaponisation would further increase as threat actors look to find novel means to bypass increasingly mature security controls at an organisation’s external perimeter, aided by threat actors maturing their automated toolkits to maximise impact upon initial access. The number of vulnerabilities in 2022 had already grown at an inexorable rate of 25 percent from the previous year from 20,171 to 25,226[3], including the SonicWall SSL VPN post-authentication arbitrary file read vulnerability zero-day (CVE-2022-22279) [4] that Dark Lab discovered in an incident response case by the LockBit Ransomware-as-a-Service (RaaS) group in March 2022 (read more here). In that case, we uncovered during our incident response that the exploit code was actively being circulated and discussed on dark web forums in February 2022 and actively weaponised by several threat actors several days after disclosure to circumvent multi-factor authentication (MFA) access controls if they had access to valid credentials.
Human-operated ransomware threat actors will increase their sophistication to make-up the shortfalls of the Crypto winter
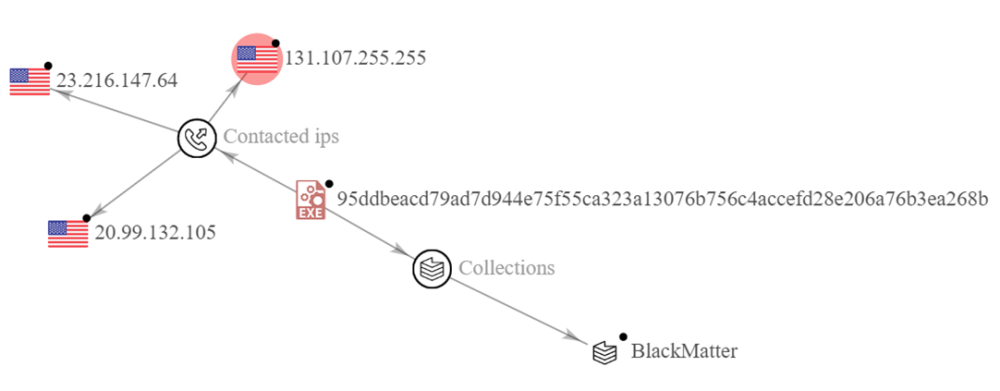
Human-operated ransomware attacks have dominated the cyber threat landscape over the past three years, booming just prior to the wake of the Covid-19 pandemic in 2020. This is largely attributed to the rise of RaaS, such as LockBit 3.0 and BlackCat who have lowered the barriers to entry for low-level threat actors by providing a subscription-based affiliate model offering custom-developed ransomware packages.
Even as the cryptocurrency markets falter, our monitoring of the overall number of listed victims on ransomware group leak sites has not dropped significantly throughout 2022. To put this into context, since the downfall of the prominent industry-leading cryptocurrency exchange FTX [5], Bitcoin and other cryptocurrencies were down almost 70 percent relative to the start of the year. However, their value remains significantly higher in comparison to 2020 levels, suggesting that ransomware groups will not disappear.
We posit that ransomware attacks will continue to rise as threat actors look to increase their victim list to make up for the staggering decline in the value of cryptocurrencies and the extreme market volatility. Simple economics suggests that threat actors would need to make up their shortfall in cryptocurrency value decline by either increasing the ransom pay-out rate (i.e., probability) or increasing the number of victims (i.e., supply). As organisations’ defenses become more advanced, cybercriminals may also need to shift to more sophisticated techniques to achieve initial access. In a recent incident response, we also observed the RaaS group Black Basta achieve initial access via a mass-scale phishing campaign before deploying ransomware (read more in a future blog post!). We expect more of the same in 2023.
The race for talent is on – threat actors are collaborating, crowdsourcing, and leveraging artificial intelligence (AI) to innovate. Enterprises will level the playing field by embracing “learn to hack” and “hack to earn” concept.
Threat actors have always been looking to gain a competitive advantage by specialising and crowdsourcing their skillsets. In 2022, our dark web monitoring allowed us to observe a 400 percent increase in listings of Initial Access Brokers (IABs), which are specialised cybercriminals that sells access to compromised networks. This outsourcing model allows other cybercriminals, such as affiliates of RaaS groups including BlackCat/ALPHV, to focus on their domain expertise (read more here). This demonstrates that this model was effective to a large extent.
However, talent has never been more scarce. Innovative threat actors have resorted to other channels for growth and inspiration. For example, other RaaS groups such as LockBit 3.0 RaaS group introduced the first bug bounty programme offered by cybercriminals. This included up to US$ 1 million for hackers of all backgrounds should they identify critical flaws in their malware, tools, or infrastructure. [6] Other threat actors have been observed from our dark web monitoring to host regular hackathons promising prize pools of up to one (1) Bitcoin for technology-specific POCs. Finally, the introduction of new tools such as ChatGPT has pushed the barrier to entry to a much lower level, and it has never been easier for script kiddies to weaponise their exploits.
We theorise that threat actors would further seek out various means to improve their competitive advantage, including collaboration and crowdsourcing. This was already an existing trend due to the RaaS affiliate model and attack-as-a-service models such as IABs, but is being disrupted by bug bounty programmes, hackathons, and artificial intelligence as a means to overcome the global cybersecurity talent shortage and skills gap. [7] As a result, enterprises are now facing an uphill battle against threat actors that are led by organisations that are harnessing the power of the people. To level the playing field, we also expect that enterprises will explore how to embrace the “learn to hack” and “hack to earn” concepts. We posit that leading enterprises will participate in bug bounty programmes and shift away from regular vulnerability scans and penetration testing to continuous assessment by bounty hunters who may not be affiliated with any vendor. Meanwhile, we also expect to see the establishment of cyber academies with the intention of democratising security through the re-skilling and upskilling pf all interested individuals regardless of their technical background. This would also provide enterprises with a new talent pipeline to ensure we have sufficient resources to fight back against “cybercriminalism”.
Web-based exploitation and targeting of individual consumers will follow-up on the hype of metaverse and the web3 ecosystem
The metaverse has quickly gone from concept to working reality in the past years. A lot of talk in 2022 was focused on simulating physical operations on the metaverse activities through games, virtual experiences or shopping with cryptocurrency and other digital assets. These experiences are underpinned by technologies such as virtual reality (VR), augmented reality (AR) devices, and artificial intelligence (AI), which naturally introduce new risks and accentuates old ones due to interoperable platforms in web3. [8] In particular, phishing email and messaging scams are already successfully leveraged by threat actors to steal passwords, private keys, personal information and money. In the metaverse, that could be even easier, especially if people think they are speaking to the physical representation of somebody they know and trust, when it could be someone else entirely. [9]
We posit that 2023 would be the year where threat actors, in particular cybercriminals, make a large jump towards targeting both businesses and individual consumers, with an increased focus to exploit web-based vulnerabilities for initial access as a result of the growing connectivity and digitalisation. We had already observed this uprising trend in late 2022 with large-scale global smishing campaigns targeting Hong Kong and Singapore citizens by masquerading as trusted and reputable locally-based public and private postal service providers (read more here). The metaverse and web3 exacerbates consumer-targeting and introduces new vulnerabilities to an increased attack surface. Aside from smart contract weaknesses, further web-application based vulnerabilities such as Spring4Shell (CVE-2022-22965) is expected to be discovered, weaponised, and utilised by threat actors to deploy cryptocurrency miners. [10] PwC’s Dark Lab had uncovered the Spring4Shell POC on the dark web two days prior to the disclosure of the zero-day vulnerability (read more here), which further emphasises on the notion that the rate of weaponisation continues to accelerate from weeks to days or even hours.
Recommendations to Secure Your 2023
There is no telling with certainty what 2023 holds, but our experience with the challenges of 2022 teach us a number of valuable lessons on how organisations can harden their cyber security posture to protect against a multitude of attack vectors.
- Grow selective hands-on technical capabilities in-house, and look to outsource and crowdsource your organisation’s security –
- Get started with bug bounty programmes: organisations should look to emulate threat actors’ by crowdsourcing specific parts of their security initiatives. In particular, organisations should explore onboarding to bug bounty programmes as it leverages the competitive advantage of the community to identify potential vulnerabilities and misconfigurations rapidly and continuously in their external perimeter. This would level the playing field, and ensure that enterprises are not alone in facing threats from threat actors groups and their affiliates by themselves. If this route were pursued, organisations should ensure they have proper governance and processes (e.g., Vulnerability Disclosure Policy) to ensure responsible disclosure of potential vulnerabilities by bounty hunters.
- Upskill and reskill your current workforce’s technical capabilities: organisations should not just rely on purely outsourcing security tasks, given there is a global shortage of talent. Instead, they should look for practical hands-on technical courses that would upskill and/or reskill their existing workforce to be more proficient in cyber threat operations, including but not limited to offensive security, security operations, incident response, threat intelligence, and threat and vulnerability management.
- Enforce a Layered Intrusion Defense Strategy
- Continuously Discover and Harden Your Attack Surface: organisations should prioritise efforts to evaluate their attack surface exposure by reviewing public-facing services and technologies in order to assess the potential risks of internet-facing services and making necessary countermeasures to eliminate the risk, such as reducing internet-exposed infrastructure, network segmentation, or decoupling the demilitarised zone from the internal network.
- Protect Privileged Accounts: as we observe threat actors pivot targeting to end users, it is critical to enforce strong credential protection and management strategies and solutions to limit credential theft and abuse. This includes leveraging technologies such as account tiering and managed services accounts, enforcing multi-factor authentication (MFA), credential hardening from privileged accounts, and regular reviewing of access rights ensuring that all practices align with zero trust and least privilege policies.
- Review and Strengthen Email Security: review current email solution configurations to ensure coverage from preventative security solutions (including external firewalls and web proxies) and implementation of conditional access rules to restrict access of suspicious activity. Consider hardening email security by leveraging artificial intelligence and machine learning technologies to augment the authentication process and create an additional barrier to restrict potential threats from bypassing detecting and delivering to the victim.
- Identifying and Protecting Critical Internal Systems: threat actors target critical systems (i.e. Domain Controllers, local and cloud backup servers, file servers, antivirus servers) that house highly sensitive information, which observed in various incidents were not protected by EDR solutions. It is crucial that organisations secure critical systems by enforcing heightened approach to devising security strategies for critical assets – including EDR, stringent patching standards, network segmentation and regular monitoring for anomolies and/or indicators of compromise.
- Defending Against Lateral Movement: the majority of threat actors moving across network rely on mechanisms that are relatively easy to disrupt with security restrictions such as restriction of remote desktop protocol between user zones, network zoning for legacy systems, segmenting dedicated applications with limited users, and disabling Windows Remote Management, among others.
- Continuously Assess your Attack Surface Exposure to understand what threats present the most prevalent challenges to your organisations and uplift preventive and detective strategies to protect against likely threats.
- Establish a robust attack surface management programme to continuously identify potential vulnerabilities on your public-facing applications, discover potential shadow IT, and stay alert to potential security risks as a result of the changing threat landscape (e.g., newly registered domains that may look to impersonate your organisation). External-facing assets should be protected with the relevant security solutions and policies to prevent, detect, and restrict malicious activity, as well as to facilitate rapid response and recovery in the case of a breach.
- Perform threat modelling to identify the threat actor groups most likely to target your region and/or sector, map your attack surface to the identified potential threats to assess how a threat actor could exploit your attack surface, and develop a plan of action to minimise that threat exposure. Regardless of whether there was a breach or not, we also recommend organisations conduct iterative intelligence-led threat hunting using the outputs of the threat modelling. As a result, the threat model also needs to be updated on a regular basis (i.e., several times a year, if not already continuously).
- Establish continuous dark web monitoring to discover if there are data breaches related to your organisation, as well as if threat actors such as IABs looking to sell access to compromised accounts and breached external assets such as web applications and web servers.
- Adopt a ‘Shift Left’ Mindset – embed cybersecurity at the forefront of innovation and implementation of new platforms, products, as well as the adoption of cloud or software solutions.
- DevSecOps: embedding cybersecurity considerations from the initial development stage enables developers to identify and address bugs and security challenges early in the development progress, strengthening the security posture of the platform to reduce vulnerabilities and attack surface exposure.
- Adoption of new technologies: the shift left mindset can also be applied to the adoption of cloud, security, and other software solutions. Organisations should be maintain oversight and awareness of new technologies being deployed in their network, assess the scope and coverage of the solutions, and subsequently develop a process to assess the security implications and risks of using these technologies.
Feel free to contact us at [darklab dot cti at hk dot pwc dot com] for any further information.